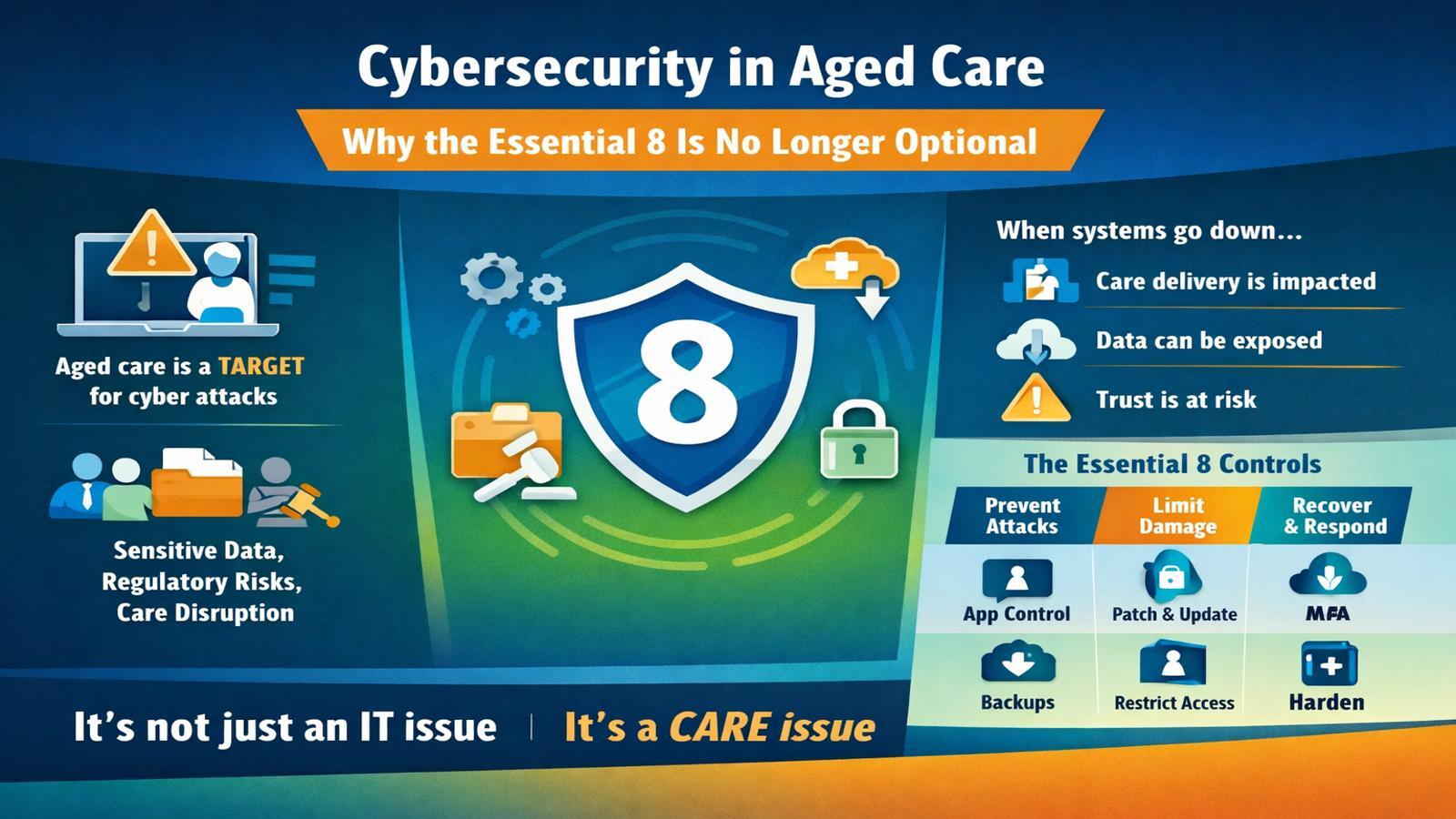
Cybersecurity in aged care is no longer just an IT conversation. It has become a direct care, governance, and leadership issue.
If your systems go down, it is not just an inconvenience. Staff cannot access rosters, medication records become unavailable, families start calling, and within hours, care delivery is impacted.
This is not hypothetical. It is already happening across the sector.
The Reality of Cyber Risk in Aged Care
Over the past few years, several major incidents have made one thing clear. Aged care and healthcare providers are being actively targeted.
Providers have had sensitive resident data exposed. Others have been hit by ransomware, forcing staff to revert to manual processes for weeks. In some cases, data has been stolen and remains permanently compromised.
These incidents highlight a pattern.
Aged care organisations are attractive targets because they hold highly sensitive data, deliver critical services, and often operate with lower cyber maturity than other industries.
The cost is not just financial. It includes reputational damage, regulatory exposure, operational disruption, and most importantly, risk to vulnerable people.
This Is Not an IT Problem, It Is a Care Problem
Picture this.
It is 7:30am on a Monday.
Staff log in and nothing works. The client management system is down. Emails are offline. Phones are ringing. No one knows where they need to be. Medication records cannot be accessed.
By 9am, you are in crisis mode. By 10am, the word ransomware is being used.
At that point, cybersecurity is no longer about technology. It is about whether you can safely deliver care.
What Is the Essential 8
The Essential 8 is a cybersecurity framework developed by the Australian Cyber Security Centre. It focuses on the eight most effective controls organisations can implement to reduce cyber risk.
At its core, it answers three simple questions.
How do we stop attacks
If something gets through, how do we limit the damage
If things go wrong, how do we recover quickly
It is not about perfection. It is about practical risk reduction.
The 8 Controls That Matter Most
The Essential 8 is structured around prevention, damage limitation, and recovery.
To prevent attacks:
Application control so only approved software can run
Patching applications to keep software up to date
Patching operating systems to close security gaps
To limit damage:
Restricting administrative privileges so not everyone has full access
Enforcing multi factor authentication across critical systems
To recover and respond:
Maintaining reliable backups that can actually be restored
Hardening user applications to block risky behaviour
Restricting Office macros to reduce common attack paths
These are not advanced controls. They are fundamentals. And yet, most breaches occur because these basics are not consistently enforced.
Understanding Maturity Levels
The Essential 8 uses a maturity model from Level 0 to Level 3.
Level 0 means there are no consistent controls
Level 1 means basic protections exist but are inconsistent
Level 2 means processes are defined but not fully enforced
Level 3 means controls are consistent, enforced, and tested
The goal is not perfection. The goal is resilience.
For aged care providers, Level 3 should be the target. It represents a position where common threats are mitigated and recovery is reliable.
Where Most Providers Actually Sit
In reality, many organisations are operating with gaps such as:
Staff can install software freely
Multi factor authentication is not enforced everywhere
Backups exist but are not regularly tested
Over reliance on IT providers without visibility of actual risk
If this sounds familiar, you are not alone. But it does mean your exposure is higher than you think.
The Questions Leaders Should Be Asking
Cybersecurity is not something you can delegate and forget. Leadership needs visibility, accountability, and confidence.
Start with these questions:
Do we know our current Essential 8 maturity level
Is MFA enforced across all critical systems
Can staff install software on devices
Are admin privileges tightly controlled
Have backups been tested recently
How long would recovery actually take
Is there a clear incident response plan
Who owns cybersecurity at an executive level
If you cannot confidently answer these, that is your starting point.
Your IT Provider Manages Technology, You Own the Risk
One of the biggest misconceptions in the sector is that cybersecurity sits entirely with the IT provider.
It does not.
Your provider manages the tools, but the organisation owns the risk, the accountability, and the consequences.
What you should expect from your provider is clear answers, evidence of controls, and a roadmap aligned to the Essential 8.
What You Can Do Right Now
You do not need to solve everything overnight. But you do need to start.
Focus on the fundamentals:
Conduct an Essential 8 assessment
Enforce MFA across all critical systems
Restrict administrative access
Implement application control
Test your backups properly
From there, build a 12 month roadmap to uplift maturity toward Level 3.
Progress matters more than perfection.
Final Thought
Cybersecurity in aged care is no longer a technical checkbox. It is about protecting people, maintaining trust, and ensuring you can continue delivering care when things go wrong.
The organisations that treat it as a leadership priority, not just an IT task, will be the ones that remain resilient.
See the slides
Latest News Posts
Loading latest blog post...
Loading additional blog posts...
